Recommendation points
Quite often, it is required to limit the circle of persons for whom access to a certain territory is allowed. Modern technology provides all the possibilities for this, those interested can get acquainted with the features of the ACS and the principles of organizing such complexes.
What is ACS
Access control and management systems are a set of hardware and software, the purpose of which is to delimit the access of people to secure facilities and territories. The operation of the system is divided into two directions: control of the unlocking of barriers installed on the main pathways, as well as maintaining a user base. The key feature of ACS is considered to be continuous operation with almost complete exclusion of the influence of the human factor.
With the first function, everything is clear: a person who wants to go through an artificial obstacle uses a personal identifier to open the passage. Admission can be carried out in all possible ways: through a password, using magnetic tags, in some cases, the system takes on a completely futuristic look using biometric scanners or face recognition algorithms.
Having a single user base is not the most obvious but often overlooked feature. Any ACS maintains a log of events, which allows you to establish with absolute accuracy at what time a certain person was in contact with the system. Due to this, the overall reliability of protection against unauthorized entry increases, in addition, there are opportunities for mutual integration with security and fire alarm systems..
Goals and objectives
Initially, ACS was developed as a means of monitoring and recording the working time of employees of large enterprises. If in the USSR these systems were exclusively “analog” and consisted of a watchman and a turnstile, then in Western countries, already 50-60 years ago, completely debugged systems with punched cards and semi-automatic readers began to appear..
One of the most iconic examples of such systems today is public access intercoms. For such purposes, security systems are installed and used for entry groups that restrict access to the courtyards of apartment buildings or cottage villages..
However, security is not the only applied task; ACS does an excellent job with commercial functions. For example, using access control, you can effectively organize the operation of paid parking lots, sublet real estate and entertainment venues..
Practical use
In the context of the sphere of construction and arrangement, ACS has not so many applications. Basically, we are talking about residents’ access to public areas or individual security systems. But there are also special cases.
For many, intercom systems have become completely familiar, thanks to which entrances have ceased to be a haven for an impartial contingent. The classic scheme for such complexes operates here: a magnetic key, a reader, an electromagnetic lock on the door. True, intercoms have an additional function of communication and remote opening, but this also applies to personal identification methods.
Another common application is equipment with access control systems for entry groups to the territory of residential complexes and private business associations. ACS in such a guise significantly increases the overall level of collective security for people and their property. The difference from intercom systems here lies only in the technical means used.
Also, access control can be applied at infrastructure facilities of housing associations. Modern apartment complexes have their own laundries, gyms, car washes and parking lots. At such facilities, the use of identifiers significantly increases the speed and convenience of providing services to the population, while the consumers themselves benefit from the convenience of payment on a single bill..
system configuration
ACS is a set of technical means used within a certain interaction scheme. Each node of the system can significantly expand its functions and capabilities, so it is worth considering the details of typical configurations.
1 – central server; 2 – router controller; 3 – video surveillance system; 4 – turnstiles and barriers; 5 – readers of personal cards and automatic locks for access to premises
The heart of any access control system is a controller that processes identification data, maintains its own operation log and maintains a user base, and also makes decisions about the operation of executive devices. The principle of building the system depends on the capabilities of the controller, in this regard, two options are possible:
- Distributed network– each security zone has its own controller that controls a limited number of readers and locks (usually up to four). The controller receives information from the reader using a special protocol (usually wiegand is used) and communicates with other system controllers via the RS-485 or RS-232 interface. User data and general system log are also stored in a distributed manner.
- Centralized network– topology with one central control unit, from which the serial interface wires are laid out along the beam pattern to each protected area. To read data and execute system commands, a switch is installed at each control point, which is essentially a combined signal converter. The difference between this scheme is that switches are cheaper than controllers, an additional plus is centralized data storage, which provides high resistance to cracking. However, due to the complex hierarchy of the network and the presence of many intermediate nodes, the performance of a centralized access control system is usually lower.
From the elements of the system with which the user interacts directly, it is possible to distinguish readers (RFID, magnetic cards and keys, radio key fobs), as well as locking devices (locks, barriers, turnstiles). In some cases, it is required to install additional sensors for the position of the door and the lock bolt. Also, since access control is usually one-way, it is usually not a reader that is installed on the opposite side of the barrier, but a conventional force-open button..
In the civilian sphere, distributed systems are still the most popular. The advantage of modern technology is that it has a monoblock design: a controller in one case with a reader and input devices. This allows you to quickly deploy the system “out of the box” without exhausting coordination of various elements and setting up the system. Such an organization scheme has only one vulnerability: physical access to the controller, but even in this case, hacking is very difficult due to the closed source firmware code and encryption of the transmitted data. In addition, the presence of at least two controllers in the network allows organizing data duplication and setting up watchdog algorithms.
Special abilities
The vast majority of access control systems with a level of complexity above the intercom are operated in conjunction with other engineering systems. The simplest example is the organization of an entry group into a private house. In this version, the access control will not only recognize the radio tag installed on the car and open the lock, but also activate the automatic gate opener and turn on the lighting. In general, the greeting algorithm can be completely varied, but the ACS controller almost never takes over the function of its execution, for these purposes there are additional PLCs.
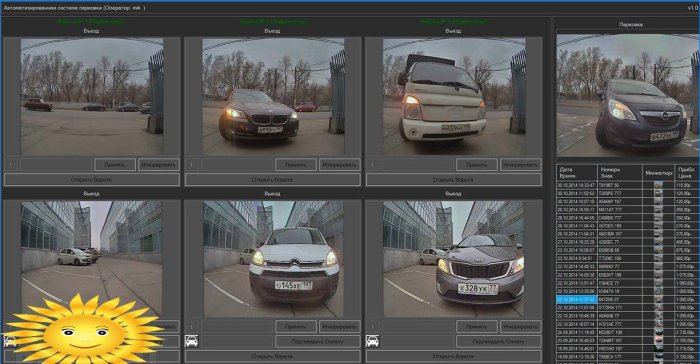
In the commercial sector and public facilities, ACS is most often mutually integrated with a video surveillance system. Due to this, it becomes possible to get out of standby mode in time and record a segment of video, capture a frame or turn the camera in the desired direction. In the most critical areas, the ACS may not make decisions on its own, sending notifications to the security console, where the operator is personally responsible for the access control based on the data provided.
Automatic algorithms are also constantly being improved. It has long been implemented and debugged schemes for prohibiting double passage and self-locking of the system when trying to access the service menu without a special key card. It is also worth mentioning that ACS takes into account in the algorithms of their work the need to ensure fire safety, opening fire exit doors in the event of an alarm, for which they use normally open electric locks..
Any access control system can be connected to an administration terminal, which is most often a PC. This method of management allows you to quickly make changes to the database: determine the circle of persons with access to a particular area of the controlled object, set additional restrictions, monitor the event log. In general, the capabilities of ACS are extremely diverse, today it is very difficult to imagine such tasks that cannot be realized with modern technical means..







What are the main features and benefits of ACS? How does ACS enhance security and streamline access management processes? Can ACS be integrated with other security systems? How does ACS handle different access levels for different individuals? Are there any specific industries or settings where ACS is particularly useful?
What are some key features of ACS (access control and management systems)? How do these systems contribute to enhancing security measures and managing entry/exit activities effectively? Can you provide any notable examples of ACS implementation in different industries?